A year ago, we released osquery to the open source community to help people detect abnormal and potentially malicious activity on Linux and OS X machines on corporate networks. Beyond sharing the tool itself, the overall goal was to create a security community where openness could thrive and provide valuable, easy-to-use resources.
Outside Facebook, osquery grew from an immeasurable amount of support from the Mac and Linux security communities. As a result of all this support and community engagement, osquery is now the highest-rated security project on GitHub, and the community is organically organizing the first osquery user forum in November.
Although Facebook has a long history with open source software (OSS) projects and communities, including React, HHVM, and Hack, we discovered some key differences in supporting an open source community in security.
Why we open-source
Facebook supports open source projects for the good of the company — it enables us to accelerate innovation, write better software, and share what we learn with others. Open collaboration helps build a project and collectively helps it grow.
Approximately 75 percent of new engineering hires are already aware of Facebook’s open source programs when they join us, and half of those employees say our efforts in open source contributed to their decision to join Facebook. This means they can use their experience with our projects right away, reducing ramp-up time while immediately contributing to open source communities both inside and outside of Facebook.
Open source and security
After 12 months of monitoring and nurturing the osquery project, we wanted to share what we’ve learned about open source communities and how they differ in security. Things like building community trust, managing build and deployment, dogfooding, and empathy stand out as critical considerations. Below are some of our recommendations for anyone who might want to create a similar community:
Know your audience and your community.
Make sure to build your project with them in mind, and test any assumptions you make. Be mindful that the hard work starts after you release your project. A constantly growing and learning environment is what the community is all about. This requires diligent and ongoing engagement to educate your audience and your team.
The traditional OSS community audience includes developers and end users, so we focused on deployment experience with osquery. However, we found that people using osquery preferred forking and maintaining internal additions, so the build tooling needs to be tailored for private repos.
Define your communication channels.
Lines of communication should be optimized for participation because without collaboration, there is no community. Democracy and empathy are important tools to have in keeping an open discussion.
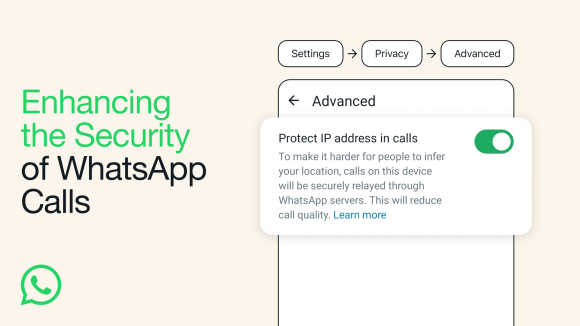
Unlike with traditional OSS, the security community often prefers private discussions because security software results are sensitive, and the use of specific software could be sensitive. In order to keep the community secure, we keep these conversations private according to the various needs of the community.
Support is important.
All open source software communities need support. Being super-responsive, especially in the beginning, is critical to creating a positive initial experience for people. It’s also important to be open and clear on any issues that arise, features you will take on, your roadmap for the future, and bandwidth to address immediate concerns — this will help avoid miscommunication with people using and contributing to your project.
With osquery, we committed to providing fresh documentation and samples as much as possible. In fact, the entire project is engineered right in GitHub so people can see exactly what we’re doing. We also discovered the importance of mentoring osquery contributors, because many of them don’t publicly share their experience with our project.
Looking ahead
Working on a security OSS community is a unique and valuable challenge. We look forward to participating in the continued growth of the open security industry by contributing future capabilities, tools, and tactics.
If you have questions about OSS in security or need help with an osquery deployment, let us know by creating an issue or emailing us.